Central bank settlement systems are the the tectonic plates of the payment system: they are vitally important to our lives, but we never see them in action. All of a nations' electronic payments are ultimately completed, or settled, on these systems. If they stop working, our financial lives go on pause, or at least regress to older forms of payment.
In this post I want to introduce readers to a crucial feature of these payments tectonic plates: their reliance for domestic settlement on SWIFTNet, a financial messaging network used by banks and other financial institutions to communicate payments information. Think of SWIFTNet as a WhatsApp for banks, but exclusive and very secure.
This reliance – or over-reliance – is best exemplified by a recent decision by the European Central Bank. The Target2 settlement system has long been the bedrock layer of the European payments universe. All domestic payment ultimately get tied-off on the system. Since it was introduced in 2007, Target2 has been solely reliant on SWIFTNet for sending and receiving messages.
When the European Central Bank replaced Target2 with T2 earlier this year, it modified the system to have two access points: it kept SWIFTNet but added a competing messaging network, SIAnet, to the mix. As one commentator triumphantly put it, "SWIFT’s monopoly for access to the T2/T2S system is broken."
SWIFTNet is owned by the Society for Worldwide Interbank Financial Telecommunication, or SWIFT, which is structured as a cooperative society under Belgian law and is owned and governed by its 11,000 or so member financial institutions. Whenever SWIFT gets mentioned in conversations, it tends to be associated with cross-border wire payments, for which its messaging network is dominant. However, for many jurisdictions, including Europe, SWIFT is also integral to making domestic payments. It's this little-known local reliance that I'm going to explore in this post.
The dilemma faced by central banks such as the European Central Bank is that SWIFTNet is an incredibly useful messaging network. It is ubiquitous: most banks already use it for cross-border payments. And so the path of least resistance for many central banks is to outsource a nation's domestic messaging requirements to SWIFT, too. However, this reliance exposes national infrastructure to SWIFTNet-related risks like foreign control, sanctions, snooping, and system outages.
Financial messaging 101
Before going further, we need to understand why financial messaging is important. For a single electronic payment to be completed, a set of databases owned by a number of financial institutions, usually banks, must engage in an intricate dance of credits and debits. To coordinate this dance, these banks need to communicate, and that's where a messaging network is crucial.
Say, for example, that Google needs to pay Apple $10 million. Google tells its banker at Wells Fargo to make the payment. Wells Fargo first updates its own database by debiting Google's balance by $10 million. The payment now has to hop over to Google Apple, which banks at Chase. For that to happen the payment flow must progress to the core of the U.S's payments system, the database owned by the Federal Reserve, the U.S.'s central bank.
Along with most other U.S. banks, Wells Fargo has an account at the Federal Reserve. It communicates to the central bank that it wants its balance to be debited by $10 million and the account of Chase to be credited by that amount. Once Chase's account at the Federal Reserve is updated, Chase gets a notification that it can finally credit Apple for $10 million. At that point Apple can finally spend the $10 million.
This entire process takes just a second or two. For this "dance of databases" to execute properly, the Federal Reserve, Chase, and Wells Fargo need to be connected to a communications network.
The sort of messaging network to which the central bank is connected, and the stewardship of that network, is thus crucial to the entire functioning of the economy.
Proprietary messaging networks or SWIFTNet?
The Federal Reserve is somewhat unique among central banks in that it has built its own proprietary messaging network for banks. All of the 9,000 or so financial institutions that use the Federal Reserve settlement system, Fedwire, must connect to the Fed's proprietary messaging network to make Fedwire payments. To make international payments, however, U.S. banks must still communicate via SWIFTNet.
Let's flesh the story out by trekking north of the border. Whereas the Federal Reserve has no reliance on SWIFTNet, Canada's core piece of domestic settlement infrastructure, Lynx, relies entirely on SWIFTNet for messaging.
For example, if Toronto Dominion Bank needs to make a $10 million to Scotiabank, it enters this order into SWIFTNet, upon which SWIFT forwards the message to Lynx, which updates each banks' accounts by $10 million and sends a confirmation back to SWIFTNet, which tells Scotiabank that the payment has settled.
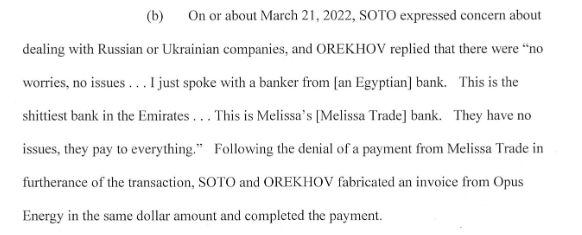
For payments nerds, this network setup is called a Y-copy topology. The network looks like a "Y" because the originating bank message is relayed from the sending bank via SWIFTNet, the pivot at the center of the Y, down to the settlement system, and then back up via SWIFTNet to the recipient bank. It is illustrated below in the context of the UK's payment system, with the CHAPS settlement system instead of Lynx, but the idea is the same.
 |
A Y-copy network topology for settling central bank payments in the UK [source]
|
The upshot is that the Federal Reserve controls the messaging apparatus on which its domestic settlement depends, whereas Canada outsources this to a cooperative on the other side of the ocean.
Many of the world's small and middle-sized central banks have adopted the same Y-copy approach as Canada. This list includes Australia, Singapore, New Zealand, Nigeria, UK, Sweden and South Africa. However, some members of this group are starting to have second thoughts about fusing themselves so completely to SWIFT.
Removing the single point of failureThe European Central Bank is at the vanguard of this group. Prior to 2023, the European Central Bank was in the same bucket as Canada, relying entirely on SWIFTNet to settle domestic transactions.
With its upgraded T2 system, Europe doesn't go quite as far the Fed's model, which is to build its own bespoke messaging network. Rather, European banks now have the option of either sending messages to T2 using SWIFTNet, or they can use SIAnet, a competing network owned by Nexi, a publicly-traded corporation. SIAnet stands for Societa Interbancaria per l'Automazione, a network that originally connected Italian banks but has now gone pan-European.
The reason for this design switch is that European Central Bank desires "network-agnostic connectivity." This dual access model will make things more complex for the European Central Bank. If a commercial bank originates a SIAnet message, the central bank will have to translate this over to a SWIFT message if the recipient bank uses SWIFTNet. Nevertheless, the European Central Bank believes this dual structure will offer more choice to domestic banks.
The ECB also hints at the enhanced "information security" that this new setup will provide, without providing much detail. The UK's recent efforts to update its core settlement layer sheds some extra insights into what these security improvements might be. Right now, the UK's core settlement system, CHAPS, can only be accessed by SWIFTNet, much like in Canada, so that all domestic UK payments are SWIFT-reliant.
In its roadmap for updating CHAPS, the Bank of England is proposing to allow banks to access the system via either SWIFTNet or a second network, which doesn't yet exist. The idea is to enable "resilient connectivity" to the core settlement layer, especially in periods of "operational or market disruption." Should SWIFTNet go down there would be no way for financial institutions to communicate with CHAPS, and the entire domestic economy would grind to a halt. A second network removes the "single point of failure" by allowing banks to re-route messages to CHAPS.
The Bank of England also highlights the benefits of competition, which would reduce the costs of connectivity.
This sounds great, but there are tradeoffs. Using a a single network for both domestic and international payments is valuable to the private sector because it offers standardization and efficiencies in banks' processing. Adding a second option will also complicate things for the Bank of England, since it will have to design and build a system from scratch, much like the Fed did, which could be costly. Either that or it will have to find another private option, like the ECB did with SIAnet. This second network may not be as good as SWIFTNet which, despite worries about resiliency, has been incredibly successful.
When CHAPS went down earlier this year for a few hours, for instance, it wasn't SWIFT's fault, but the Bank of England's fault. The same goes for a full day outage in 2014.
 |
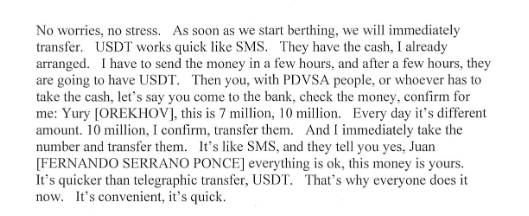
Comparing a V-shaped network topology to Y-Copy in an Australian context [source]
|
The type of settlement topology that the UK is proposing is known as "V-shaped," since all messages are sent directly to the central bank settlement system for processing via any of a number of messaging networks, and then back to the recipient bank. The difference between a V-shaped topology and Y-copy is visualized in the chart above in an Australian context, but the principles apply just as well to the UK.
Sanctions and "the SWIFT affair"The decision to make domestic payments less dependent on SWIFTNet is much more easy to make for outlier nations like Russia. SWIFT is based in Belgium and
is overseen by the Belgian central bank, along with the G-10 central banks: Banca d’Italia, Bank of Canada, Bank of England, Bank of Japan, Banque de France, De Nederlandsche Bank, Deutsche Bundesbank, European Central Bank, Sveriges Riksbank, Swiss National Bank, and the Federal Reserve. That put SWIFT governance far out of Russian control.
You can see why this could be a problem for Russia. Imagine that only way to settle domestic Russian payments was by communicating through SWIFTNet. If Russia was subsequently cut off from that network for violating international law, that would mean that all Russian domestic payments would suddenly cease to work. It would be a disaster.
Needless to say, the Central Bank of Russia has ensured that it doesn't depend on SWIFTNet for communications. It has its own
domestic messaging network known as
Sistema peredachi finansovykh soobscheniy, or System for Transfer of Financial Messages (SPFS), which was built in 2014 after the invasion of Crimea. Prior to then, it appears that "
almost all" domestic Russian transactions passed through SWIFTNet
– a dangerous proposition for a country about to face sanctions.
Mind you, while Russia has protected its domestic payments from SWIFTNet-related risk, it can't do the same for its international payments. SWIFTNet remains the dominant network for making a cross border wire. There is no network the Russians can create that will get around this.
I'm pretty sure that most larger developing states and/or rogue nations have long-since built independent domestic financial messaging systems to avoid SWIFTNet risk. I believe China has done so. Brazil has the National Financial System Network, or
Rede do sistema financeiro nacional (RSFN). India also has its own system, the
Structured Financial Messaging System (SFMS), built in 2001. India is even
trying to export SFMS as a SWIFT competitor.
The Japanese were typically way ahead on this. The Bank of Japan
built its messaging network, the Zengin Data Telecommunication System, back in 1973, several years before SWIFT was founded.
The last SWIFTNet risk is snooping risk. This gets us into the so-called
SWIFT affair. After 9/11, the U.S. intelligence agencies were able to pry open SWIFT through secret
broad administrative subpoenas. They had the jurisdiction to do so because one of SWIFT's two main data centres was located in the U.S.
To ensure data integrity, SWIFT had been mirroring European data held in its data centre in Belgium at its U.S. site. That effectively gave U.S. intelligence access to not only SWIFT's U.S. payments information, but also information on foreign payments sourced from Europe or directed to Europe. Worse, it also provided spooks with data on domestic European payments. Recall that the European Central Bank's Target2 settlement system, which settles all digital domestic payments in Europe, was entirely reliant on SWIFTNet for communications.
When the U.S.'s snooping arrangement was
made public by the New York Times in 2006, it caused a huge controversy in Europe. SWIFT tried to placate Europe by
building a third data warehouse in Switzerland to house Europe's back-up data. But the precedent was set: SWIFT is not 100% trustworthy. And that may be part of the reason why the European Central Bank chose to downgrade its reliance on SWIFTNet when it introduced its new system, and is surely why other nations want to entirely hive their domestic systems off from it.
---
In sum, central banks face a host of complicated decisions in how to bolt on messaging capabilities to their key settlement systems. SWIFTNet is a top notch network. However, too much SWIFT-related risk may be perceived as having negative implications for national security. For large nations with extensive banking industries, building a proprietary domestic messaging alternative seems to be the preferred option. It also seems to be the default choice for rogue states like Russia.
Another alternative is to fallback on using multiple independent networks for access, of which one is SWIFTNet, and thus mitigating exposure to SWIFT-related problems. This is the approach taken by Europe and the UK.
For smaller nations that comply with the global consensus, like Canada, the calculus is different. Building an alternative communications network is likely to be costly. The risk of sanctions and censorship are negligible while the benefits of using a high-quality ubiquitous network for both domestic and foreign payments messaging are significant. Given these factors, it may be worthwhile to bear all SWIFT-related risks and adopt the Y-copy model.